In October 2017, it was reported that a National Security Agency (NSA) contractor in 2015 had compromised inadvertently the agency’s software both for protecting U.S. networks and for penetrating those of others. The story is interesting not only for the reported damage, which could be considerable, but also because it hints of ongoing cyber warfare and the mechanisms used to steal NSA’s secrets.
A widely reported survey suggests that as many as 30 percent of people will open so-called phishing emails and attachments, which can plant malicious software or trick people into revealing sensitive information such as passwords.1 Such software, for example, may count and identify key-strokes a person uses to log on to the system, allowing an attacker to gain full access. Hence the emphasis on sweeping computer networks to detect unauthorized software and changing passwords frequently.
The current case is more disturbing: the contractor broke NSA rules by taking work home. He seems to have imagined that he was protecting his home computer adequately by using top-of-the-line antivirus software, in this case from Kaspersky Lab, a U.S. subsidiary of a company headquartered in Moscow with alleged ties to the Russian government. Kaspersky’s software, like most antivirus programs, flags suspicious code on scanned drives and uploads it to the company’s network for (in theory) examination by company analysts. The company’s end-user license agreement—which users rarely if ever read—explicitly allows such copying. Around the time the story broke, the NSA publicly banned Kaspersky antivirus programs from sensitive U.S. computers, without saying why. The company strongly denied the implication that it was working for the Russian government. The October report may be the NSA’s way of justifying itself in pressing for the ban.
It is difficult to imagine how a software company operating in Russia would be able to resist government pressure to share information it obtains. The Russian Federation lacks a clear rule of law to protect private companies from such interference. Company founder Yevgeny “Eugene” Kaspersky attended the Institute of Cryptography, Telecommunications, and Computer Science in Moscow, known before the collapse of the Soviet Union as the Technical Faculty of the KGB Higher School. After graduating in 1987, he served as an intelligence officer in the Red Army. It is possible he never dropped (or was permitted to drop) his intelligence connections. It is difficult to imagine that the KGB’s successors—the Federal Security Service and the Foreign Intelligence Service—could or would resist the temptation represented by a computer security system that normally and legitimately extracts data from the computers on which it is installed around the world.
The story is disturbing in light of recent public NSA history. Edward Snowden was an NSA contractor who might himself be described as a malicious virus. He has said that he joined the agency specifically to attack it. He managed to concentrate considerable material on a thumb drive and take it home. About a year after Snowden publicly denounced the NSA, and gave newspapers much of the material he had stolen, it was reported that NSA software intended to penetrate foreign computer systems had been compromised and was being offered for sale on the dark web. Reports suggest some of this software was used in a massive blackmail attack on Western computers, including those running various European hospitals. Snowden denied having been the source of the penetration software, but he may be lying. That he has found refuge in Russia suggests he has been willing or compelled to work with Russian intelligence against the NSA.
The compromised NSA materials also are said to have included software intended to protect U.S. computer networks against foreign attack. In recent years there has been much discussion of the vulnerability of the U.S. economy and of critical U.S. infrastructure to computer attack. U.S. utilities, for example, are linked by the internet. The U.S. financial system works largely through the internet, and vulnerability increases as the U.S. economy comes closer to becoming cash-free. The “internet of things,” including items as diverse as driverless cars, washing machines, coffee makers, and televisions, creates new vulnerabilities. In theory, malicious software could be designed to target individual appliances, or to use the plethora of computer-linked cameras and microphones to spy on anyone. These devices present both risk and opportunity to the NSA. As internet-enabled products find their way into other countries, they become potential sources of intelligence.
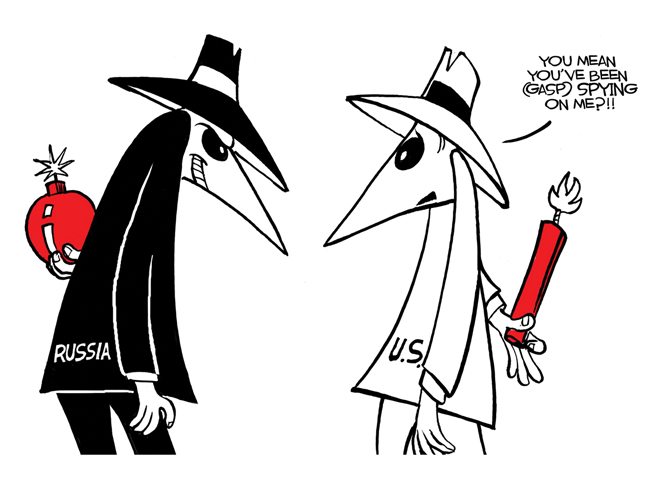
The other side of the story is that it confirms that the NSA has been seeking to penetrate foreign computer networks. The NSA’s network penetration software shows the vast changes from the agency’s past work breaking codes and monitoring radio and telephone communications. Successful network penetration should make it possible to collect considerable intelligence describing foreign weapon systems and technological developments, the sort of material that in the past came from human intelligence sources. Such considerations make NSA more and more important in the battle against technologically advanced potential enemies.
Those who look to U.S. internet vulnerability generally assume that, as the most technologically advanced country, the United States is uniquely vulnerable. We have entered a new era in which cyber attack can have great strategic consequences. Public knowledge that the NSA is working on penetration of foreign networks may in itself have a deterrent effect. The key to strategic coercion is not how much physical damage an attack can do; it is how seriously the target takes that potential damage. At the same time, this latest story of an NSA contractor willfully mishandling classified information points to the serious damage that can be done by an insider threat.
1. Wombat Security Technologies, “The State of the Phish,” www.wombatsecurity.com/press-releases/new-report-state-of-phishing-attacks.



