Late Winter 2021
After the USNS Comfort departed New York in April 2020, Xuehua Peng began his underwater reconnaissance. A graduate student born in the United States, Peng purchased several GPS-guided unmanned underwater drones with integrated fish-finding sonar to build precise maps of the Manhattan Cruise Terminal seafloor. The drones cost just $1,000 each, and their lithium batteries provided two hours of bottom time at speeds up to 8 knots. Peng’s research professor, also affiliated with China’s Ministry of State Security, ensured Peng received full departmental sponsorship, but the Port Authority raised few questions. In broad daylight, the drones built contour maps with millimeter precision.
As COVID-19 cases spiked in winter 2021, the Comfort returned to the Manhattan Cruise Terminal to support the hospital system. Peng deployed his scout drone. At the designated waypoint, it dove toward the river bottom. The integrated sonar enabled the drone to slip beneath the port security barrier. Bottlenose dolphins from the Navy’s Marine Mammal Program patrolling the water for unauthorized swimmers immediately detected the probing drone. When the dolphins challenged the drone, contact sensors released paralyzing toxins from the towed fishing bait container. After toxin release, a single line of code prompted the drone to surface and begin recording ultrahigh-definition video. Two minutes later, a wolf pack of drones followed their GPS waypoints toward the hospital ship. Each carried a 7-kilogram shaped charge. The observer drone recorded as the shaped charges detonated against the Comfort’s shaft staves.1 Peng’s scout drone live-streamed the explosions and watched as the Comfort’s stern dropped deeper into the water. Emergency responders rushed to the scene, but the engineering spaces flooded too rapidly. Peng collected his scout drone and slipped south on the Hudson River.
Consecutive Chiefs of Naval Operations have designated unmanned undersea vehicles (UUVs) as necessary for the strategic objectives of the Sea Services; however, U.S. adversaries also recognize the potential of these platforms.2 Since 2015, the commercial unmanned systems industry has produced numerous inexpensive, small UUVs (sUUVs). The low cost and rapidly increasing capability of these drones represent an emerging and potent asymmetric threat to high-value maritime assets. The Sea Services must counter the sUUV threat by raising threat awareness, modeling physical security, deploying networked undersea sensors, and dominating UUV employment.
Understanding the Threat
Size, Weight, and Power (SWAP). The small unmanned aerial system (sUAS) industry optimized SWAP for drone batteries, and these batteries give sUUV manufacturers a running start.3 In addition, positively buoyant sUUV bodies do not have the burden of staying aloft, so their thrusters maintain depth while sipping only small amounts of power. Commercial vendors typically leverage the same battery components across unmanned system classes, and the same battery that keeps a two-pound sUAS flying for 20 minutes can power a 14-pound sUUV for four hours.4 Once at desired depth, variable speed horizontal thrusters supply efficient propulsion and tight handling. For example, Youcan Robot BW Space Pro’s largest-in-class battery supplies power to the vehicle’s thrusters for three to five hours.5 Given that additional battery cells could be added with neutral buoyancy, engineers could cheaply extend sUUV endurance.
Sensors and Robotics. Advances in parallel industries delivered cheap sensors and robotic extensions equivalent to advanced military hardware to sUUV designers. Depth sensors enable auto depth control, and multiple vertical thrusters provide auto pitch control. For sensing the environment, the standard for sUUV optics is a 12-megapixel camera that shoots 4K ultrahigh-definition video, and most sUUVs can transmit sensor data to multiple devices via Chinese-made 5G WiFi repeaters.6 Integrated fish finders such as the Powervision PowerSeeker act as chin-sonar arrays, and artificial intelligence (AI) software builds detailed underwater topographic maps.7 Beyond sensing the environment, robotic appendages interface with the environment. Many sUUVs include towed fish bait containers that release payloads on operator command or at designated coordinates. Articulating arms also can be added to sUUVs such as the Geneinno Titan.8 Titan and other similar sUUVs allow a drone operator to achieve effects at greater than 100 meters, more than three times deeper than scuba divers.
Underwater Autonomy. sUUV vendors have fewer regulations on GPS-enabled control software compared with the Federal Aviation Administration’s (FAA’s) strict control on unmanned aerial systems.9 Most sUUVs are tethered, but, in practice, this is not an unbreakable bond. The Powervision Power-Dolphin allows operators to build untethered search tracks with GPS waypoints. Onboard fish finders also could enable navigation based on bottom depth, and onboard inertial measurement units (IMUs) like those on the Sea-Drone Inspector 3 precisely track the vehicle’s orientation across nine degrees of freedom (three axes for gyroscope, accelerometer, and compass).10 Even without a continuous GPS signal during submerged operations, the combination of reference coordinates at submergence, IMU awareness, and bottom contour sensing offer the needed ingredients for autonomous submerged navigation.
Data Exploitation. Concerns over data capture by foreign-made drones is well documented in government and industry.11 Users of sUUVs potentially could pass mapping information through Chinese servers, inadvertently generating high-fidelity contour maps of U.S. inland and coastal waters. And that is not the only vector of data vulnerability. For initial setup, most sUUVs require the user to download firmware from the internet. This typically requires contacting a server at the manufacturer’s headquarters (usually in China) to receive a multigigabyte download.12 During operation, the user interfaces with the sUUV through a smartphone application. This offers a potential view of the sUUV user’s contacts and other personal data.13 After using sUUVs, most users save their drone’s data to their personal computers. Direct interface between the drone, smartphones, personal computers, and the internet is an invitation for data exploitation.14
The undersea lacks defense-in-depth strategies compared to other domains. The 2018 Winter Olympics in South Korea opened with an orchestrated performance of 1,218 Intel Shooting Star sUASs. As fans enjoyed the light show, security professionals broke out in cold sweats. Small, cheap, and autonomously guided drones challenge defense-in-depth strategies across all domains. Commercial vendors soon will be able to provide the same type of swarm coordination undersea.
For U.S. enemies, the undersea will be more challenging than other domains to exploit because of water clarity, signal attenuation, refraction, and a host of other factors, but defending against sUUVs also will be more difficult. Aside from the natural obstacles, few layers of defense exist in the undersea. Previously, credible undersea threats came from UUVs such as the reported Russian Kanyon.15 But these large UUVs need water deep enough for submerged navigation, which limits the possible vectors of attack. With sUUV proliferation, the inland waterways and littoral seas face new, potentially potent entrants. sUUVs such as Chasing’s Gladius Mini can generate effects in shallow or deep water, changing the threat calculus.16 Inland, sUUVs could jeopardize the $4.6 trillion in annual economic activity generated by the U.S. Maritime Transportation System.17
Lack of Legal Construct for Effective Regulation. Legal frameworks treat the majority of international and inland waterways as public commons, which translates to a more permissive environment. For example, while the FAA regulates the aerial commons by altitude, few regulations exist for undersea depth separation. The U.S. Coast Guard is the executive agency for maritime law enforcement in the United States, but the absence of undersea regulations limits its efficacy. In addition, autonomous navigation packages using a combination of an initial GPS fix and inertial or bottom contour guidance will neuter GPS-based regulations such as those implemented by the FAA for unmanned aerial systems.
Practical Approaches
Raise Threat Awareness. Using the plan, practice, perform, progress, promulgate (P5) cycle, operational commanders should generate plans to counter sUUVs and test these plans with Red Cells. The Sea Services should practice joint defense-in-depth at places such as ballistic missile submarine bases: Marine Corps security battalions secure the ground; Navy personnel provide security forces for each hull; and Coast Guard Maritime Force Protection Units provide escort during transit. The Marine Corps already employs Red Cells for deployment certifications, and the Sea Services should expand this practice.18 Aggressive Red Cells can identify vulnerabilities and inspire new doctrine for sUUV offense and defense. Objective advisors from institutions such as the Army’s University of Foreign Military and Cultural Studies (“Red Team University”) should monitor the P5 cycle and recommend improvements to executive stakeholders.19
Model Physical Security. Borrowed from systems engineering, modeling shifts the traditional paradigm of design-build-test to model-analyze-build. This allows programs to prototype, experiment, and test solutions before they are delivered to the warfighter.20 The Sea Services should use a model-based approach to integrate joint contributions in the undersea. Given the recent arrival of sUUVs, legacy programs of record lack requirements to counter sUUVs or integrate with counter-sUUV systems. A model-based analysis would simulate existing capabilities to counter sUUVs and inform capability gap analyses.21 In addition, a mature model would enable efficient integration of the lessons learned from the Department of Defense’s (DoD’s) and FAA’s experience in countering sUASs.
Modeling also could identify opportunities for scale. Methods such as SSBN bases provide localized security around high-value targets, but such a manpower-intensive strategy will be unsustainable across the 120,000 miles of U.S. shoreline and inland waterways.22 The Coast Guard possesses the legal authorities to defend the homeland from sUUVs, but it has limited experience in the undersea.23 A model-based approach would identify support needed from DoD, domestic law enforcement, and coalition partners. It also would reveal recommendations for regulations for sUUV vendors and U.S. smartphone application marketplaces.
Deploy Networked Undersea Sensors. The Sea Services should deploy networked undersea sensors that enable manned and unmanned teams to increase the area monitored and decrease the size at which sUUVs become detectable.24 The United States has decades of experience monitoring the undersea for large manned submarines, but current systems are not optimized for sUUVs. Facilities such as the Atlantic Undersea Test and Evaluation Center could help develop sensor suites that maintain three-dimensional awareness of the ocean environment.
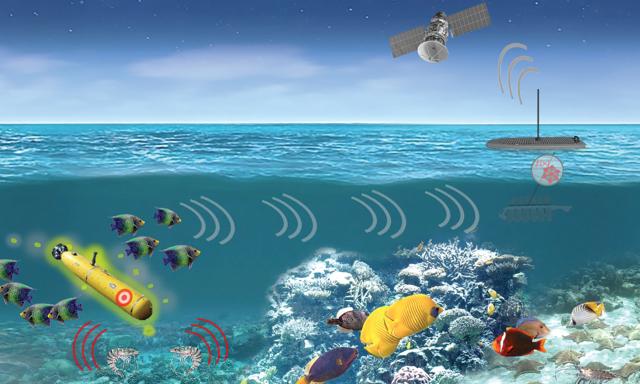
To defend against sUUVs, proven technologies will need to be managed by manned and unmanned teams. Unmanned systems using AI and machine learning should detect sUUVs and federate with national assets such as the Integrated Undersea Surveillance System. In addition, the Sea Services should identify ways to further integrate marine life into their sensor network. The Navy’s Marine Mammal Program has trained dolphins and sea lions to perform undersea missions for decades, and this type of man-animal-machine teaming should be expanded.25 As an illustration, the Defense Advanced Research Projects Agency’s Persistent Aquatic Living Sensors program offers opportunities to integrate marine organisms in the threat-recognition cycle.26
Dominate UUV Employment. The best way to maintain undersea superiority is to dominate all classes of UUVs. Organizations with UUV expertise should be identified and reinforced at the strategic, operational, and tactical levels for great power competition. At the theater strategic level of war, combatant commanders must coordinate U.S. and coalition forces to deny adversaries the ability to achieve effects with sUUVs.
The Navy’s Program Executive Office for Unmanned and Small Combatants (PEO USC) provides the strategic-level leadership to identify requirements and spend acquisition dollars efficiently across the enterprise. In addition to UUV development, PEO USC should work with other program offices to ensure legacy platforms can launch UUVs and coordinate their operations. It also should leverage the proposed model-based analysis to define requirements for new acquisition programs and upgrade existing platforms and should coordinate requirement generation with the Joint Requirements Oversight Council to avoid duplicating capability across the services.
At the operational level of war, the Navy’s UUV Squadron and Submarine Development Squadrons should develop doctrine for UUV dominance. Satellites, ships, and radars monitor the oceans’ surface, but the sensor-per-area ratio is significantly different for undersea monitoring. New insights will be critical to raising domain awareness, as thermal strata, depth, and other factors offer layers of shadow for sUUVs. Development squadrons should partner with cross-domain ranges such as the Advanced Naval Technology Exercise and the Chief of Naval Operations’ Task Force Ocean.27
At the tactical level, the Sea Services need the Joint Staff to endorse tactics, techniques, and procedures for UUV operations. With requirements similar to the Joint Unmanned Aircraft Systems Minimum Training Standards, the services should develop specific qualification programs similar to the basic UAS qualification.28 Given the diverse and growing family of UUVs in the portfolio, the services need uniform training standards to build competency in UUV and counter-UUV operations. Also, the Naval Air Training and Operating Procedures Standardization (NATOPS) manual is worthy of emulation. Just as NATOPS promulgates and deconflicts UAS policies and operations and those of manned flight, the Sea Services should develop standards to ensure effective waterspace management and prevent mutual interference between manned and unmanned systems.
Responding to the Threat
On 11 September 2001, terrorists used manned commercial aircraft to ignite a generation of conflict. Today’s sUUVs offer even more credible and potent asymmetric threats, and the capability of sUUVs will continue to grow as the cost of dual-use technologies drops. They pose a new array of threat scenarios, and the Sea Services must develop strategic, operational, and tactical responses.
1. Shaft staves keep seawater from entering the hull.
2. ADM Michael Gilday, USN, “FRAGO 01/2019: A Design for Maintaining Maritime Superiority,” December 2019.
3. Tuna Toksoz, Joshua Redding, Matthew Michini, Bernard Michini, and Jonathan P. How, “Automated Battery Swap and Recharge to Enable Persistent UAV Missions,” Massachusetts Institute of Technology, March 2011, 1, https://core.ac.uk/download/pdf/191015665.pdf.
4. Powervision PowerRay Product Specification, www.powervision.me/eu/product/powerray/specs.
5. Youcan Robot, “BW Space Pro User Manual,” www.youcanrobot.com/support.
6. Youcan Robot, “BW Space Pro Product Description,” https://store.youcanrobot.com/details/BW-Space-Pro-4K-Zoom.
7. Powervision PowerDolphin product specification, www.powervision.me/en/product/powerdolphin/specs.
8. Geneinno Titan product specification, https://geneinno.us/products/geneinno-t1.
9. Federal Aviation Administration, “Unmanned Aircraft Systems,” 24 July 2020, www.faa.gov/uas/.
10. SeaDrone, Inspector 3 product specification, https://seadronepro.com/inspector-3#inspector-3-specs.
11. American Security Drone Act, introduced, www.congress.gov/bill/116th-congress/senate-bill/2502.
12. Author email correspondence with Youcan Robot Customer Support in Shanghai, China, 2 January 2020.
13. Parth Misra, “All the Ways in Which Your Smartphone Can Track You and How to Put an End to It,” Entrepreneur, 11 December 2018.
14. Cybersecurity and Infrastructure Security Agency, “Cybersecurity for Electronic Devices,” 15 November 2019, https://us-cert.cisa.gov/ncas/tips/ST05-017.
15. Joshua Portzer, “Kanyon’s Reach: Rethinking the Nuclear Triad in the Autonomous Age,” U.S. Naval Institute Proceedings 146, no. 7 (July 2020).
16. Chasing, Gladius Mini product specification, www.chasing.com/gladius-mini.html.
17. U.S. Coast Guard, Maritime Commerce Strategic Outlook (Washington, DC: Department of Homeland Security, October 2018), 3.
18. LCDR James Landreth, USN, and CAPTs Shelby Ochs and Matthew Riloff, USMC, “The Marines and the Future of Unmanned Systems,” blog post, Defense Acquisition Magazine, May 2020, 23.
19. For more information on the UFMCS, see https://usacac.army.mil/organizations/ufmcs-red-teaming/.
20. Office of the Deputy Assistant Secretary of Defense for Systems Engineering, Digital Engineering Strategy (Washington, DC: Department of Defense, June 2018), 15.
21. U.S. Navy and Marine Corps Digital Systems Engineering Transformation Strategy 2020 (Washington, DC: Department of the Navy, 2020), 26.
22. U.S. Coast Guard, Maritime Commerce Strategic Outlook (Washington, DC: October 2018), 3.
23. LCDR James Landreth, USN, “Coast Guard Role in the Great Power Competition,” Defense Acquisition Magazine, January 2020, 40.
24. Office of the U.S. Air Force Chief Scientist, Autonomous Horizons: The Way Forward (Air University Press, March 2019), 38.
25. “U.S. Navy Marine Mammal Program,” www.public.navy.mil/navwar/NIWC-Pacific/technology/Pages/mammals.aspx.
26. Defense Advanced Research Projects Agency, “Five Teams of Researchers Will Help DARPA Detect Undersea Activity by Analyzing Behaviors of Marine Organisms,” 15 February 2019, www.darpa.mil/news-events/2019-02-15.
27. Naval Undersea Warfare Center Newport Division, “Advanced Naval Technology Exercise 2020,” Naval Sea Systems Command, www.navsea.navy.mil/Home/Warfare-Centers/NUWC-Newport/What-We-Do/ANTX-2020/.
28. Joint Staff, Joint Unmanned Aircraft Systems Minimum Training Standards (Washington, DC: 4 September 2012), 2.