Two Internet incidents earlier this year, revealed only in October, suggest previously unappreciated vulnerabilities. In one, a mass of Internet traffic, particularly that with U.S. military addresses, was routed through China for about 20 minutes. In another, Internet users in the United States and Chile found it impossible to contact certain Web sites that the Chinese government has deemed to be politically unacceptable to its own population. Neither incident involved a virus like the Stuxnet, designed specifically to attack Iranian centrifuges. Rather, each seems to have made use of the basic characteristics of the Internet itself.
This is a very important difference. Governments will use Internet vehicles, such as viruses and worms, to attack enemies by penetrating apparently secure sites. That is like past attempts to intercept and decode radio traffic, or to tap international cables. Such attempts have a long history, and it is not too difficult to imagine modern equivalents of earlier countermeasures.
However, many also imagine that the Internet itself is so universally valuable that no rational government would seek to destroy or damage it. Yet that is exactly what the Chinese government seems to have done. The Internet relies on a basic structure of trusted computers (servers). A message sent into the Internet goes to the nearest server, which decides, among other things, which server to pass it to for onward transmission. The Internet as a whole is highly decentralized, because it was designed initially to operate effectively even if many of the servers were destroyed. Thus the system seeks the most efficient transmission path. Typically, messages are chopped into small slices so that communication channels can be used most efficiently; the destination computer reassembles them. If your Internet connection is slow enough, you can actually see this process taking place on your screen, culminating in the “done” message.
The Internet attempts to move messages as quickly as possible; each server in the chain is always looking for the shortest path forward, which often is not the shortest from a geographical point of view. For example, quickness depends on how many messages the various servers in the path must handle. Physical path length is not all that important for messages traveling at the speed of light. Some of the best paths undoubtedly pass through China, though it seems unlikely that one from, say, one U.S. computer to another would typically do so.
When you type an Internet address onto your computer, it must be converted into what amounts to the phone number of the intended recipient. Conversion is done by dedicated computers holding what are essentially telephone directories, though on a massive scale. It is tacitly assumed that no one would be foolish enough to tamper with such directories; surely it is in everyone’s interest that Internet messages flow to their intended destinations.
A New Great Wall
This assumption apparently is not true for a Chinese government fearful that free access to information is subversive (and the Chinese government surely is not alone in this view). That government has therefore erected a kind of internal Great Electronic Wall. A Chinese civilian trying to get to a blocked Web site finds his computer redirected to a government site. Redirection is achieved by manipulating the address books used by Chinese Internet servers. The same software could be used to select other Internet traffic of particular interest, highlighting it for (say) duplication and retention.
American and Chilean users probably ran afoul of the Chinese re-addressing technique when their messages passed through China: any message passing through that country could fall victim to the Great Electronic Wall. Making that happen on a large enough scale to be noticeable would suggest that the Internet message-transmission scheme itself had been subverted. It might even be that the blockage of many U.S. and Chilean messages to particular Web sites was a test of the technique later used to divert masses of U.S. Internet messages of potential interest to the Chinese.
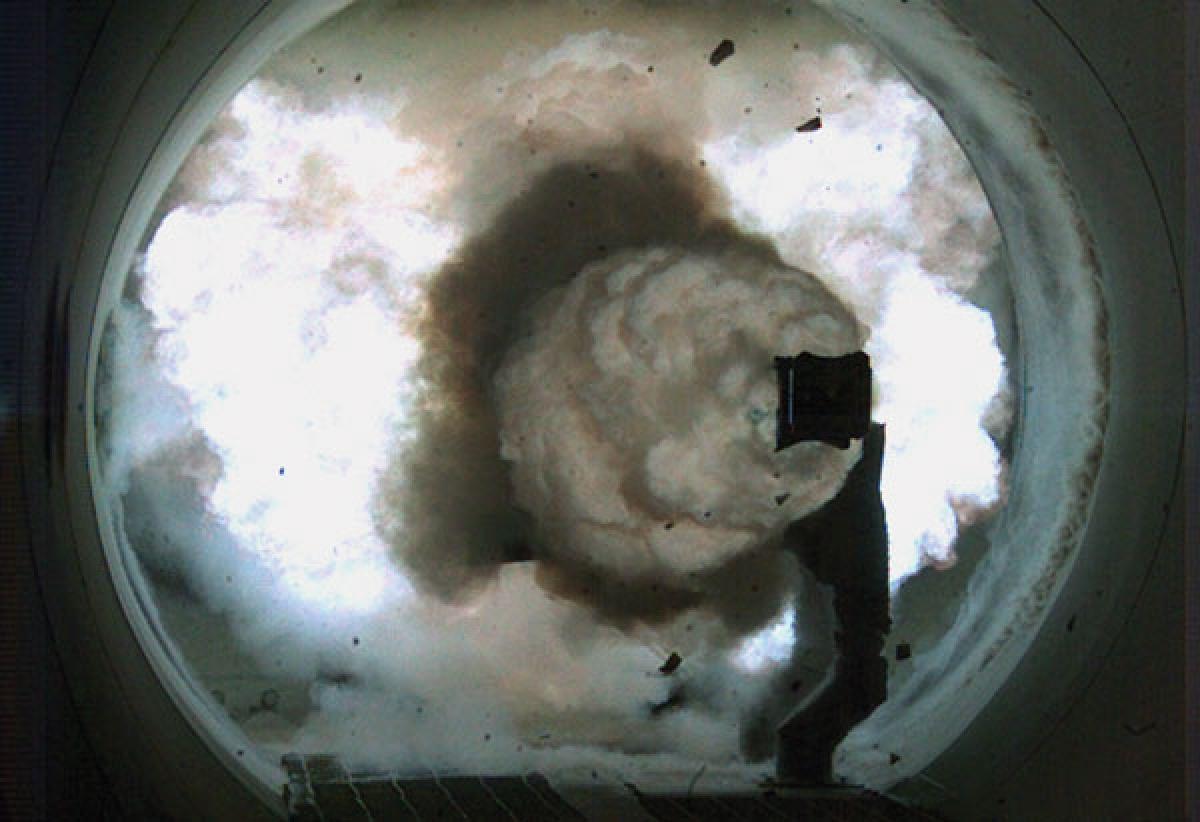
Servers on the Internet decide how to transmit messages by estimating the delays inherent in different alternative paths. They make those estimates on the basis of “advertisements” of path length (in terms of time) produced by other servers along different possible message paths. The Internet cannot work efficiently if this technical data is somehow corrupted. The assumption is that no one would interfere with the basic structure of the system. However, it now appears that the Chinese decided that it was worth their while to break the rules in spectacular fashion. Servers in China advertised very short transmission times so as to capture the desired traffic. Perhaps they restricted such advertisements to traffic with particularly desirable identifiers, such as the .gov and .mil suffixes used for U.S. military and governmental traffic. For about 20 minutes, until the distortion was detected by Internet administrators, the traffic flowed through Chinese servers.
Those who announced the event refused to speculate about its purpose, if any, but the possibilities are unsettling. It is not clear how easily a Chinese server could insert unwanted software, such as a trapdoor, in material passing through it, but it does seem that whatever traffic passed through Chinese servers could have been automatically copied and saved.
To the extent that classified U.S. communications traffic passes through the civilian Internet in encrypted form, the maneuver gave the Chinese a mass of material, much of it encrypted using the same key (keys change over time), perhaps to a depth sufficient for break-ins. The object of the operation may have been to gain enough insight into the kind of traffic involved that special software could be inserted during a future diversion. Again, the short duration and the sheer mass of material involved suggests that it would not have been possible this time to eliminate particular messages—unless this was not the first such attempt. Because it is not clear how the victims discovered the problem, it cannot be said with certainty that this was the first time.
Fair Game?
The incident is particularly interesting because it brings into question the idea that such international utilities are so universally valuable that no one will vandalize them for national ends. For example, surely no one would attack the Global Positioning Satellite system directly, because everyone benefits from it. Some enemy might jam the system locally, of course, to deny U.S. forces its value in particular battles, but developing and fielding systems to shoot down the satellites would surely be pointless. During World War II, the British decided not to attack the German radio navigational system (Consol) operating over the Bay of Biscay precisely because they found it useful for their own operations, and this example is often cited.
Similar reasoning is often used to deny the possibility that any government would begin shooting down reconnaissance or other satellites—surely the effective truce in space benefits all governments with the ability to do so, because all such governments also use space for their own purposes, and all would suffer if it were open season on satellites. During the Cold War, the U.S. government watched the Soviets experiment with antisatellite weapons. When the experiments ended, the U.S. interpretation was that the Soviets had realized it was best not to attack space assets, because their own were so valuable. Only later did it become clear that the experiments had ended when the Soviet antisatellite system was deemed mature enough to be accepted into service. It was operational exactly when U.S. government analysts thought it had been discarded. Ignorance of the Soviet reality probably made the Chinese antisatellite test a few years ago more surprising than it should have been. Moreover, the Chinese test might be seen as somewhat analogous to the Internet attacks this year—a willing attack on something thought to be safe because everyone benefited from it.
There is another way to interpret both the satellite and Internet attacks. If the Chinese had to fight the United States, such attacks might indeed be deeply counterproductive. However, the Chinese leadership may be more interested in intimidation. If it can demonstrate an apparent ability to cancel out some of our technology, then it may imagine that it can convince, say, the Taiwanese or even the Japanese that the United States cannot protect them. The Chinese may think that many in East Asia will feel compelled to come to terms with them. The publicity given to the antiship ballistic missile (DF-21D) may fall under the same heading. In each case, it is easier to assert a Chinese capability than to make the limits of that capability obvious. Since the Chinese do not expect to have to prove anything by fighting, the argument that subverting the Internet is counterproductive may not mean much to them.
For our part, it is time to understand that at least one, and probably other, governments supplying Internet resources may find cyber-attack more important than access to the Internet itself. Perhaps it is time to invest enough to separate classified traffic physically (not merely by encryption) from the civilian Internet. We may also want to develop, or demonstrate, an ability to defend our satellites from attack, or at the least to replace them as rapidly as an enemy attacks them. On a larger scale, we certainly want to demonstrate that the Chinese cannot sap our command-and-control and reconnaissance abilities. We may already believe that our systems can survive, but we need to make that more obvious to our friends—and our enemies.