U.S. armed forces are dependent on a complex system of interwoven networks—e.g., transportation, telecommunications, financial—for all of their activities, and will be more so as network-centric warfare evolves. Knowing their vulnerabilities is essential.
The Navy and the Department of Defense are in the midst of fundamental changes in mission, force structure, tactics, and doctrine—all driven by the services' shift from platform-centric warfare to network-centric warfare. Writing in the January 1998 Proceedings, former Director for Space, Information Warfare, Command and Control Vice Admiral Art Cebrowski and John Garstka, a technical advisor for the Joint Chiefs of Staff Directorate for C4 systems, identified a logical model for this network-centric approach. They depict a high-performance information grid that provides a backplane for communications and processing and enables the operational sensor and engagement grids. This model, which addresses the war fighters' reliance on the unprecedented flow and processing of timely, reliable information, is too narrow.
The flow of information, services, and resources depends on a complex system of interwoven networks within the United States and host countries, not just on the communications grid. These networks—telecommunications, electrical power, petroleum, transportation, potable water, financial, etc.—support much more than the exchange of information and the employment of weapon systems. They are used by DoD during the execution of all of its activities. Daily operations and tactical, operational, and strategic actions all are dependent on the uninterrupted availability of infrastructure networks and the commercial/civilian resources on which they are built.
DoD must realize that these infrastructure networks are key vulnerabilities. The National Command Authorities already have established the multiagency Infrastructure Protection Task Force (IPTF) to identify and coordinate existing expertise and capabilities in government and the private sector to counter both physical and cyber threats. And President Bill Clinton, speaking at the U.S. Naval Academy, stated that he was signing two presidential decision directives that "call for a national effort to ensure the security of the increasingly vulnerable and interconnected infrastructures of the United States [including] telecommunications, banking and finance, energy, transportation, and essential government services.” It is questionable, however, that the operational and tactical communities have the same appreciation of network interdependencies, let alone the plans to deal with offensive and defensive network-centric operations on a global scale.
Threat
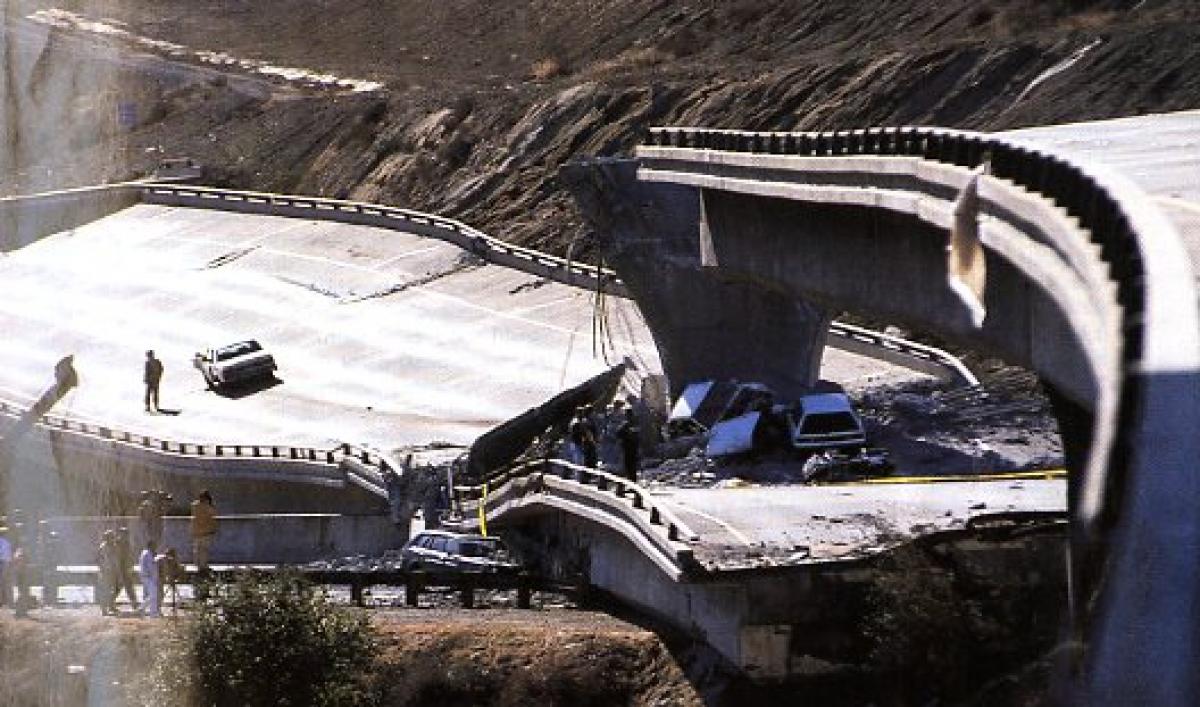
The denial of any one infrastructure network may not in itself be a knockout punch, but when infrastructure network denial is considered in the context of overall military operations, reduced force structure, and a growing number of commitments, it may well be a tactical—if not a strategic—rabbit punch. The recent perturbations to pagers and financial transactions caused by the misalignment of the Galaxy-4 communications satellite illustrate how dependent the United States has become on supporting networks.
Designing and building a fleet without appreciating this threat, however ill defined, is a prescription for disaster. Regional conflicts are increasing. World events have proved that terrorists can strike anywhere at any time. We could face foreign intelligence operatives directed against sensitive infrastructure network nodes, inadvertent interference or interruptions, specious hacking, and political or economic terrorism. The United States no longer can assume that it is a sanctuary.
Winn Schwartau, writing in Information Warfare, notes that the Federal Bureau of Investigation believes there are 200 former Afghan fighters living in the New York-New Jersey area, and many of them may be acting on behalf of the anti-Western Iranian government. He also quotes the report "Terrorism in the USA," prepared by the House Task Force on Terrorism and Unconventional Warfare, which states, "There has been a concentrated effort by Iran and Syria, and to a lesser extent Libya, with extensive professional help from Cuba and North Korea, to consolidate terrorist infrastructure in the U.S." This includes economic threats such as counterfeiting and drug-related activities aimed at the overall security of the United States. During crisis or regional conflict, we also could encounter physical or electronic attack and destruction by national or terrorist entities, attempts to seize or disrupt key network control nodes, use of directed energy or special technology devices, employment of jamming and deception, and information/data warfare.
The threat is such that the Justice Department has created a domestic counterterrorism office. Attacks on the Federal Reserve and the air traffic control systems, for example, would have a significant impact on domestic stability and national security. Though not traditional military targets, the various components of the United States' and the West's infrastructure network may fall increasingly within an enemy's cross hairs. This multipolar, often unconventional threat—when coupled with the growing dependence of inter-theater command and control, deployment, and sustainment on global, commercial lines of communications—is alarming. Author Alan D. Campen notes that during Desert Shield and Desert Storm virtually all of the long-haul telecommunications of the Free World were brought together, yet even when functioning at design speeds in an undisturbed environment, some systems trailed a giant step behind customer demands.
Joint Operations
Concepts that exploit technology, such as the Cooperative Engagement Capability and Joint Composite Track Network, Ring of Fire, and Information Technology-21, are well-known warfighting examples of the current revolution in military affairs. But lesser-known examples are having the same type of impact. The logistics and force deployment communities are just as involved in this revolution. FM 100-5, Operations, and PAM 525-5, Force XXI Operations, outline how future forces will be built around a split-based, fully integrated structure.
This will be a truly joint force, dependent on networked infrastructures from the factory all the way to the foxhole. According to General Jack Sheehan, former Commander-in-Chief, U.S. Atlantic Command, it will depend more than ever on commercial augmentation, such as strategic and tactical lift, communications, and a full range of logistics items. Already, 95% of U.S. armed forces communications flow via commercial networks.
As the joint force responds to given missions around the globe, the limitations of strategic and commercial lift assets will require that we use the time-phased force deployment (TPFD) planning tools. The ability to mobilize, deploy, and sustain a force depends on the unique capabilities of DoD's logistics systems—which are moving rapidly from just in case" support to a just in time" system that mimics private enterprise, and is wholly dependent on networked infrastructures.
All military facilities in the United States depend on commercial power. The movement of forces from depots, forts, and bases to air and sea ports of embarkation, and from these ports of debarkation into the theater, is conducted primarily via commercial transportation.
Military-owned strategic airlift assets (C-5, C-141, and C-17 cargo planes) and long-range bombers (B-52s and B-1s) can fly from U.S. bases directly to theater, but this capability depends on the availability of aerial refueling assets, which are forward deployed at bases on foreign soil. Naval battle groups can be replenished under way, on-station in theater, but the fuel, stores, and refit sites that support this capability are housed on foreign soil and are dependent on host-nation infrastructures. Even the formidable carrier battle group becomes vulnerable when its support ship is attacked in a foreign port.
The lack of U.S. shipping during Desert Shield and Desert Storm—only about 300 commercial ships remain under U.S. flag—forced the Military Sealift Command to have U.S.-flag ships unload their cargoes in Aljiciras, Spain, where they were reloaded on foreign-flag vessels for shipment into theater. Even prepositioned stores, including those in climate-controlled warehouses ashore and in unarmed ships afloat, depend on host-nation infrastructure.
Theater commanders-in-chief need to know when and how their forces will arrive. They need to know what Achilles' heels may exist in their deployment plans. They need a thorough understanding of what options are available should the TPFD execution process become snarled. Will the expected order of battle be available on time, and sufficiently armed and supplied? How vulnerable are key through points in Spain, Germany, and Japan? During the Gulf War, an Iraqi ballistic missile attack on Al Jubayl, Saudi Arabia, scored a near miss at this key port of debarkation. At the time, four cargo ships, a U.S. helicopter carrier, two aviation support ships, and an Army barge were alongside the pier, where hundreds of vehicles and tons of munitions were being processed. These and other sites are not impervious to terrorist or other anti-- United States acts.
Many questions must be answered today, to avoid confusion and possible disaster tomorrow. What roles do civil infrastructure networks play in support of joint military actions? Who is responsible for the defense of the United States and the U.S. civil infrastructure? What are the roles of the federal and state governments and private concerns? The unified commanders-in-chief and joint DoD organizations are responsible for specific portions of the infrastructure that the military uses—Transportation Command for transportation; Defense Information Systems Agency for information/communications; Forces Command for military support for civil authorities; the Defense Special Weapons Agency for force-protection surveys on certain DoD facilities, etc.—but there is no integrated approach to identifying and quantifying the vulnerabilities of key networks and the critical roles they play with regard to joint force operations.
Planning for Network Casualties
Identifying and evaluating the vulnerability of critical infrastructure networks from a systems-effect perspective must be done in conjunction with existing strategic, operational, and tactical planning. Data bases of key assets and infrastructure exist today both inside and outside DoD (e.g., Federal Emergency Management Agency, Departments of Energy, Commerce, and Justice, etc.). Integration of these analysis tools and data bases should be initiated to support this planning.
The impact of infrastructure network casualties is not always obvious. Operational mission planners may not realize that a power outage or computer system compromise that occurs hundreds of miles away from a key port or airport of debarkation can have ripple effects that reach all the way to in-theater, tactical operations. The ability to analyze, assess, and quantify the strategic and tactical implications of adverse infrastructure network actions also is needed. A relevant set of metrics must be developed to achieve this. Automated, graphical, modeling, and simulation tools should be integrated with war gaming, mission planning, and command-and-control systems such as the Global Command and Control System and the Global Support System.
Planners need to know what options are available to mitigate adverse effects and restore network infrastructure capabilities. The options could range from simple modifications in tactics, doctrine, and training to the development of complex node hardening of critical infrastructure components. Ensuring that training exercises such as emergency deployment readiness exercises are conducted realistically and under stressful infrastructure denial environments will help prepare war fighters to deal with crisis situations. How many personnel-recall exercises have been conducted without telephones? Modifying and expanding existing national security policy can help address infrastructure concerns. The response options must be strong and include military, civil, and private/industrial input.
The Navy and joint forces are dependent on infrastructure networks today, and they will be more so tomorrow, as network-centric warfare evolves. The operational roles that such networks play must be known and quantifiable. Infrastructure networks must be examined and appreciated as the interwoven enabler of military missions, and military leaders must appreciate their complexity, as well as their vulnerability. Used creatively, they can provide tremendous offensive capability.
Mr. Podlesny is an electronics engineer at the Naval Surface Warfare Center, Dahlgren, Virginia. He works on battle management C4ISR issues related to littoral and expeditionary warfare, special operations, and missile defense.